The great hope of the 1990s and 2000s was that the internet would be a force for openness and freedom. As Stewart Brand, a pioneer of online communities, put it: “Information wants to be free, because the cost of getting it out is getting lower and lower all the time.” It was not to be. Bad information often drove out good. Authoritarian states co-opted the technologies that were supposed to loosen their grip. Information was wielded as a weapon of war. Amid this disappointment one development offers cause for fresh hope: the emerging era of open-source intelligence (OSINT).
This quote, from an article in The Economist, describes a field most people have never heard of. Indeed, I was totally unfamiliar with OSINT until quite recently, when I kept seeing the term being used on social media.


Then, I read a glowing review online about a recently published book, We Are Bellingcat.
I read the book, and frankly it blew my mind. What is it about? A section of the book jacket description reads:
We are Bellingcat tells the inspiring story of how a college dropout pioneered a new category of reporting and galvanized citizen journalists- working together from their computer screens around the globe- to crack major cases, at a time when fact-based journalism is under assault from authoritarian forces. Founder Eliot Higgins introduces readers to the tools Bellingcat investigators use, tools available to anyone, from software that helps you pinpoint the location of an image, to an app that can nail down the time that photo was taken.
This technique, collecting and analyzing data from resources open to the public, is known as open source intelligence, or OSINT. What would be the purpose of such an activity? We Are Bellingcat focuses on some of the group’s most important investigations: the downing of flight MH17 over Ukraine, Assad’s use of chemical weapons in Syria and the identities of alt-right protesters in Charlottesville, Virgina. As they explain in a website post for people interested in learning the basics:
The promise of open source research is that anyone — not just journalists or researchers at select institutions — can contribute to investigations that uncover wrongdoing and hold perpetrators of crimes and atrocities to account.
When we say “anyone”, we mean anyone: if you’ve an internet connection, free time, and a stubborn commitment to getting the facts right, then you too, can be an open source researcher.

Columbia Journalism Review (CJR) published an article discussing terrorism and the Christchurch mosque shooting specifically and they noted:
Bellingcat…produced a comprehensive and contextualized report on the motives and movements of the Christchurch killer before he carried out the attacks. The piece contextualized his use of internet image boards and the references he made in his writings and video.
“His manifesto is not dangerous to the average reader,” Bellingcat’s Robert Evans, who wrote the piece, tells me. “The people who will be most influenced by the details of this are people who are already in the dark corners of the internet and already know.” Evans would not have posted Tarrant’s writing whole or uncontextualized, “but pointing out things he feels are important, what radicalized and influenced him is important.”
Another important figure in the realm of OSINT is Christiaan Triebert.


Born and raised in the Netherlands, Triebert was involved at Bellingcat during the website’s earlier years, and created a crucial toolkit for OSINT researchers (see tweet below). Among many other functions, such programs allow the user to track the course of specific planes and ships.


Triebert now works for the New York Times, using his research/analytical skills to help produce their acclaimed Visual Investigations series. The following information/article was released as I write this, from another staff member at the NYT.


The Visual Investigations team has done reports on everything from the horrific mass shooting in Las Vegas to the murder of journalist Jamal Khashoggi in Saudi Arabia. The video/documentary where the team studies the Jan 6 insurrection is the their masterpiece, though, and is on the shortlist for an Academy Award nomination (documentary short).
Speaking of Jan 6, Triebert is not the only person who has used OSINT methods to take a closer look at the attack.




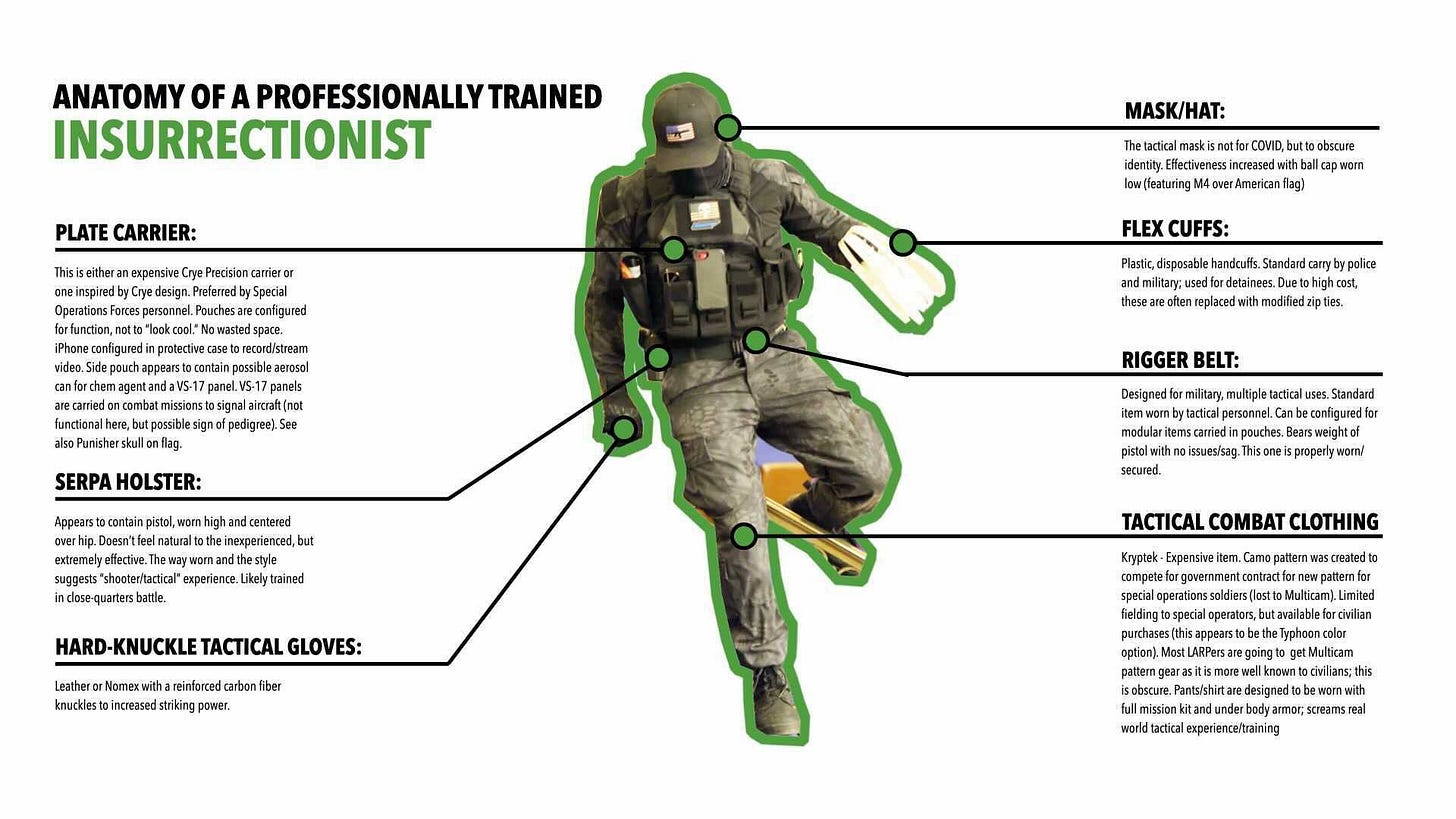
An army of so-called online sleuths, known as #seditionhunters, have assisted law enforcement in helping to identify people who broke the law that day, an operation that has become one of the biggest manhunts in history.






An article in the Daily Kos explains:
John Scott-Railton is a senior researcher at the University of Toronto’s Citizen Lab, and swiftly identified Brock after image enhancement software made his outfit’s flair recognizable. There was the Texas flag patch, and even more helpful, there was the yellow fleur de lis of the 706th Fighter Squadron. Scott-Railton wasn’t the only person in what he calls the “digital ecosystem of accountability” to track Brock down, either: Michael Sheldon, of the Atlantic Council’s Digital Forensic Research Lab, also identified the 53-year-old father of three who lives in an affluent part of the Dallas metro area.









Gisela Pérez de Acha is an attorney/reporter originally from Mexico, who has written on extremism and other topics.
She became so fascinated with the field of open source research that she started teaching a college level course in the topic. J298 OSINT Seminar- Open Source Investigations, at The University of California at Berkeley Graduate School of Journalism, teaches how to incorporate traditional investigative reporting with the latest OSINT methods. The schools website explains:
This class will be two part: a seminar focusing on a particular story in collaboration with the Associated Press, and a lab portion focusing on using cutting edge Open Source investigative techniques, pioneered by Berkeley’s Human Right’s Center, with investigative reporting and multimedia skills. This course will be co-taught by representatives from the Human Right’s Center, the Investigative Reporting program and Richard Koci Hernandez, with the objective of producing high-quality OSINT Investigations. AP journalists will also likely contribute to this seminar.


Finally, the investigative news site ProPublica has released a new mapping tool that looks at the persistent health/cancer risks that residents in certain areas have long faced due to pollution.


The Houston Chronicle notes:
The reporters explain how their work is especially important because it shows on a granular level what is known as the "cumulative" effects of pollution from all industrial facilities in an area, rather than a single facility on its own. The journalists spent two years analyzing an enormous amount of emissions data from a five-year span. ProPublica calls the final product "the most detailed map of cancer-causing industrial air pollution ever published." It's not meant to be a definitive indicator for any single case of cancer, they explain, but rather a resource for people to understand better the risks of where they live.
ProPublica has also been involved in investigating the capital insurrection: see here.